Margin Research Blog
Writings on Security, Research, and Technology
smoothie_operator<<
Description This blog details a C++ heap exploitation challenge written for CSAW CTF Finals 2022. This challenge incorporates an OOB heap write primitive to corrupt heap metadata, creating a use-after-free (UAF) by clobbering the C++ std::shared_ptr struct. The challenge is a x86-64 ELF binary linked against glibc v2.

Russia’s Open-Source Code and Private-Sector Cybersecurity Ecosystem
Through our work on SocialCyber, we map sanctioned Russian cyber actors, their contributions to the linux kernel, and the private-sector firms supporting Russian cyber operations.
An opinionated guide on how to reverse engineer software, part 2
The best reverse engineer is also a very capable software developer. Why you may ask? Because almost no one reinvents the wheel.

Winternships and a new look
The website has gotten a facelift! If you've been to our site before you might notice some changes. The most significant change is in our blog backend, making sharing our great research and new tool releases easier with the internet. Another big shift is consolidating all of our
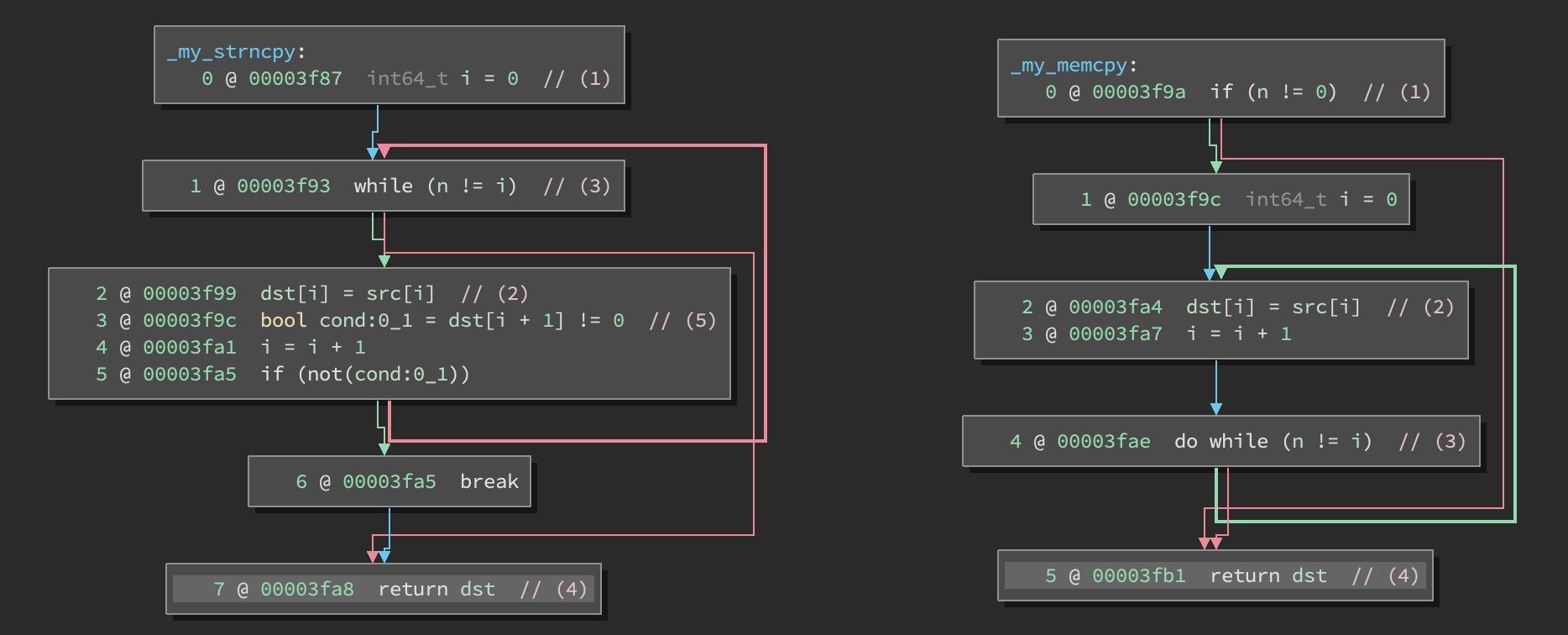
Pulling MikroTik into the Limelight
A comprehensive guide to MikroTik internals, including IPC, hand-rolled cryptography, and a novel post-authentication jailbreak
Cannoli: The Fast Qemu Tracer
Cannoli Cannoli is a high-performance tracing engine for qemu-user. It can record a trace of both PCs executed as well as memory operations. It consists of a small patch to QEMU to expose locations to inject some code directly into the JIT, a shared library which is loaded into QEMU

The Chinese Private Sector Cyber Landscape
As China's "decade-long quest to become a superpower" comes to fruition, the PRC has increasingly moved to eliminate barriers between its civilian-commercial industries and the State.
Watching the Watchers
Much of our world relies on open source projects. The Linux kernel is arguably the crowning achievement of the open source movement, the foundation of Google’s Android and NASA’s satellite software. But five of the top ten bug reporters are automated systems.
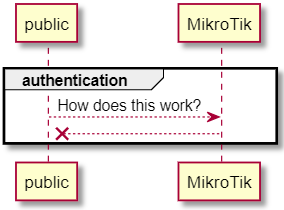
MikroTik Authentication Revealed
A deep-dive into MikroTik's hand-rolled Elliptic Curve Secure Remote Protocol (EC-SRP) cryptography used in client-server authentication